SharpClipHistory
Overview
Users regularly copy to their clipboard sensitive data such as usernames and passwords. This makes the clipboard history valuable to attackers when gathering information in order to perform post exploitation activities such as lateral movement. As a result, storing the entire clipboard history could be dangerous and allow attackers to gain access to sensitive data.
However, Microsoft has introduced a new feature in Windows 10 (build 1809) called Cloud Clipboard:
https://community.windows.com/en-us/stories/cloud-clipboard-windows-10
tl;dr "If you choose to enable syncing, you can access your copied content from any Windows device you’re logged into and add or modify it at a moment’s notice. You can review what you copy in the clipboard history viewer, hold multiple pieces of text and images there, and share them with any other Windows devices you’re logged into."
Traditional approaches to accessing clipboard content commonly involve monitoring for copy events and reactively sending new clipboard content to the attacker. However, this does not enable access to past clipboard content and requires continuous monitoring over a long period of time. Using the Cloud Clipboard feature, we can now make a simple call to a UWP API method and get content from across the entire history of the clipboard.
To abuse this functionality, MWR has introduced SharpClipHistory. The tool is a .NET application written in C# and can be used to retrieve the entire clipboard history contents along with the date and time when each entry was copied.
Starting with Windows 10 Build 1809 the feature is present but it is up to the user whether it is enabled. This can be done either via the GUI that can be accessed using WIN+V or by modifying a registry key in HKEY_CURRENT_USER :
C:\Users\user>reg query HKEY_CURRENT_USER\Software\Microsoft\Clipboard /v EnableClipboardHistory
HKEY_CURRENT_USER\Software\Microsoft\Clipboard
EnableClipboardHistory REG_DWORD 0x1
If the Cloud History feature is disabled, SharpClipHistory can be used to enable it by changing the above registry key value.
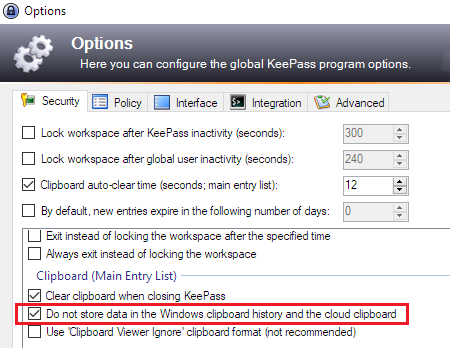
This tool can be used to obtain copied passwords from most password managers. However, some of them, like KeePass, understand that the Cloud Clipboard feature is dangerous and have released an update to avoid storing copied passwords. This security control can be found in the KeePass options as illustrated below:
In order to bypass this, SharpClipHistory terminates all running KeePass instances and modifies the KeePass configuration file by adding the following line to %APPDATA%\Roaming\KeePass\KeePass.config.xml:
<Security>
[redacted]
<ClipboardNoPersist>false</ClipboardNoPersist>
</Security>
The next time that KeePass is launched, all copied passwords will also be stored in the clipboard history.
Example
beacon> execute-assembly /root/SharpClipHistory.exe
[*] Tasked beacon to run .NET program: SharpClipHistory.exe
[+] host called home, sent: 224299 bytes
[+] received output:
[+] Clipboard history feature is enabled!
[+] Clipboard history Contents:
4/25/2019 7:25:11 PM Sup3rS3cr3tPassw0rd123!
4/25/2019 7:25:06 PM admin