Microsoft Office 365 Message Encryption Insecure Mode of Operation
Overview
Microsoft Office 365 Message Encryption (OME) utilitises Electronic Codebook (ECB) mode of operation. This mode is generally insecure and can leak information about the structure of the messages sent, which can lead to partial or full message disclosure. As stated in the NIST’s "Announcement of Proposal to Revise Special Publication 800-38A": "In the NIST National Vulnerability Database (NVD), the use of ECB to encrypt confidential information constitutes a severe security vulnerability; for example, see CVE-2020-11500."
Description
Microsoft Office 365 offers a method of sending encrypted messages. This feature is advertised to allow organization to send and receive encrypted email messages between people inside and outside your organization in a secure manner. Unfortunately the OME messages are encrypted in insecure Electronic Codebook (ECB) mode of operation.
Impact
Malicious 3rd party gaining access to the encrypted email messages may be able to identify content of the messages since ECB leaks certain structural information of the messages. This leads to potential loss of confidentiality.
Since the encrypted messages are sent as a regular email attachments, the messages sent may be stored in various email systems, and may have been intercepted by any party between the sender and the recipient.
An attacker with a large database of messages may infer their content (or parts of it) by analyzing relative locations of repeated sections of the intercepted messages.
Most OME encrypted messages are impacted, and the attack can be performed offline on any previously sent, received or intercepted encrypted messages. There is no way for the organization to prevent analysis of already sent messages, nor does use of rights management features remediate the problem.
Depending on the content sent via encrypted messages, some organizations may need to consider legal impact of the vulnerability. It is possible that vulnerability has lead to privacy impact as described in EU General Data Protection Regulation (GDPR), State of California Consumer Privacy Act (CCPA), or some other similar legislation.
Details
Electronic Codebook (ECB) mode of operation means that each cipher block is encrypted individually. Repeating blocks of the clear text message always map to the same cipher text blocks. In practice this means that while the actual cleartext is not revealed directly, information about the structure of the message is. Here is a RAW image that has been AES encrypted in ECB mode of operation:
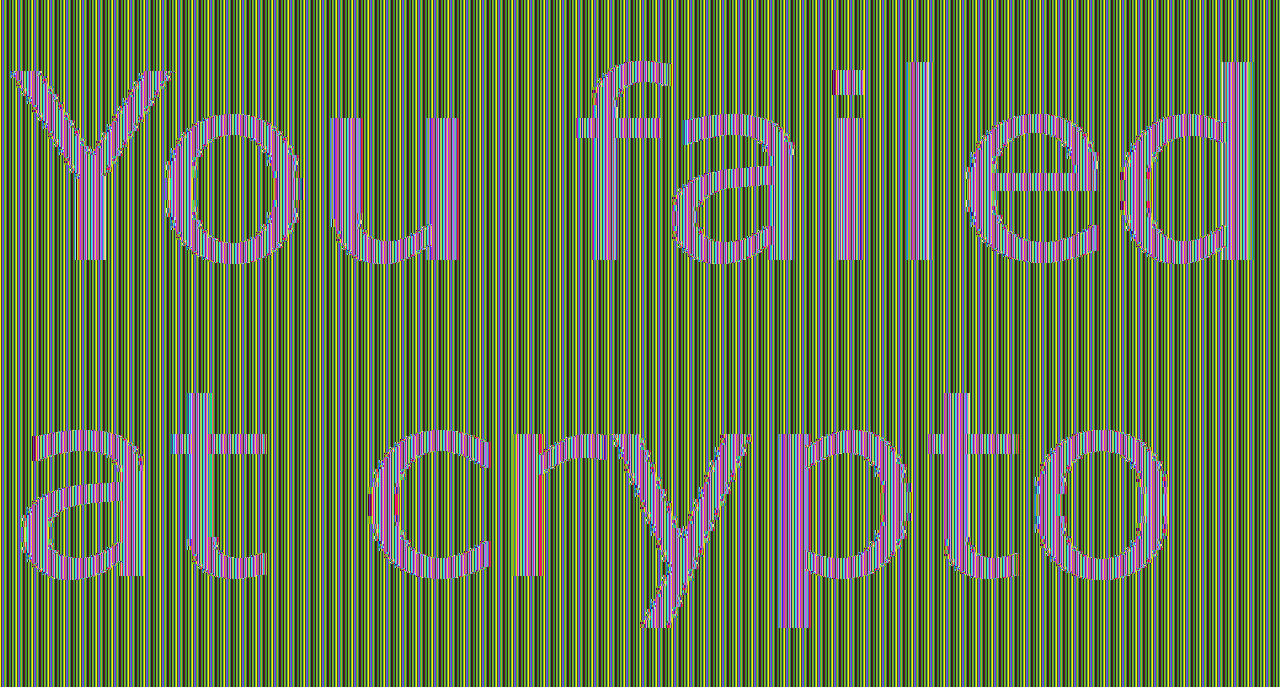
While the actual individual pixel values are not known, the actual image content can be easily identified.
Even if specific message would not directly leak information in this way, an attacker with a large body of messages is able to perform analysis of the relation of the repeated patterns in the files to identify specific files. This may lead to ability to infer (parts of) clear text of encrypted messages.
No knowledge of the encryption key is required to exploit this vulnerability and hence Bring Your Own Key (BYOK) or similar encryption key protection measures have no remedial impact.
The cipher used for Microsoft Office 365 Message Encryption appears to be Advanced Encryption Standard (AES). However, in the context of this vulnerability the actual cipher is irrelevant since the ECB mode of operation has the same properties regardless of the cipher used.
CWE-327: Use of a Broken or Risky Cryptographic Algorithm
Outlook 365 Message Encryption uses Electronic Codebook (ECB) mode of operation when encrypting the message into RPMSG blob.
The root cause for the vulnerability appears to be a prior decision to use Electronic Codebook (ECB) mode of operation with message encryption and then maintaining compatibility with this poor decision.
The Microsoft Information Protection (MIP) ProtectionHandler::PublishingSettings class has a SetIsDeprecatedAlgorithmPreferred method (1) that is documented as:
"Sets whether or not deprecated crypto algorithm (ECB) is preferred for backwards compatibility."
It is likely that OME uses this method to enable the ECB encryption of RPMSG. If this flag is not set Cipher Block Chaining (CBC) mode of operation is used.
Microsoft Information Protection FIPS 140-2 Compliance (2) documentation mentions that
"Legacy versions of Office (2010) require AES 128 ECB, and Office docs are still protected in this manner by Office apps."
Remediation
After repeated queries about the status of the vulnerability Microsoft eventually replied with the following:
"The report was not considered meeting the bar for security servicing, nor is it considered a breach. No code change was made and so no CVE was issued for this report."
End user or administrator of the email system has no option to enforce more secure mode of operation. Since Microsoft has no plans to fix this vulnerability the only mitigation is to avoid using Microsoft Office 365 Message Encryption.
Partial Mitigation
Some exchange online plans offer "Microsoft Purview Advanced Message Encryption". When available, this feature can be configured to enforce sending only a link to the OME portal, and omit the RPMSG attachment.
Such configuration can be deployed by following the Microsoft Instructions on how to ensure all external recipients use the OME Portal to read encrypted mail. More specifically: New-TransportRule must be deployed with -ApplyRightsProtectionTemplate "Do Not Forward". Once deployed it is recommended to verify the correct operation by sending an encrypted email to an external email address to ensure that no RPMSG attachment is sent.
This mitigation has the drawback of being available only to certain enterprise level plans. Furthermore, it doesn't help against an adversary who can intercept the pin code email sent to the recipient of a pin-protected OEM email, and it doesn't solve potential issues with the email messages sent prior to the configuration change.
Special thanks to Marko Buuri from Fraktal Oy for help in crafting this mitigation.